Enable and configure SSL post installation#
Enabling SSL#
Because Package Security Manager (On-prem) does not require SSL certificates to operate, you’ll need to perform some additional steps in order to enable SSL on an existing HTTP based instance.
Log into your instanace of Package Security Manager as a user with root access.
Open your Package Security Manager installer directory. This directory contains both the
docker-compose.ymland.envfiles.Tip
You can find your installer directory by running the
ls -lacommand to view the contents of your current working directory.# Replace <INSTALLER_DIRECTORY> with your base installer directory cd <INSTALLER_DIRECTORY>
Edit your
docker-compose.ymlfile.Find the
Services:section near the top of the file. Then, under thenginx_proxy:portion, add the following lines:secrets: - source: nginx_key target: /etc/nginx/certs/tls.key - source: nginx_cert target: /etc/nginx/certs/tls.crt
Find the
Keycloak:section further down in the file. Then, under theenvironment:portion, add this line:- PROXY_ADDRESS_FORWARDING=true
Edit your
.envfile.Change
DOMAINto new FQDN, if applicable.Change
NGINX_PROXY_PORTto443.Change
PROTOCOLtohttps
Configuring SSL#
The following steps will allow you to configure the SSL:
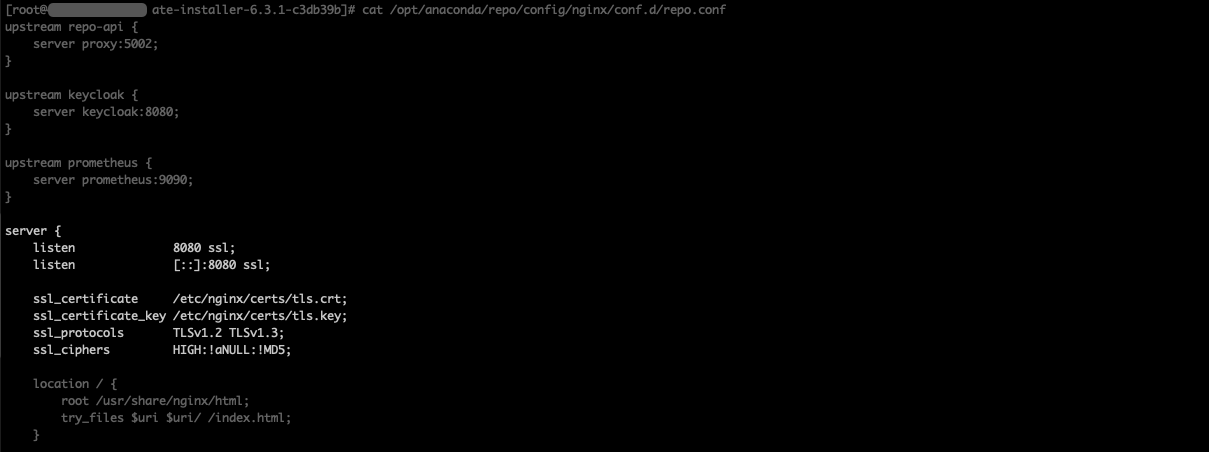
Add or remove the following lines relating to the SSL in
<BASE_INSTALL_DIR>/config/nginx/conf.d/repo.conf, where<BASE_INSTALL_DIR>is the installation directory:listen 8080 ssl; ssl_certificate /etc/nginx/certs/tls.crt; ssl_certificate_key /etc/nginx/certs/tls.key; ssl_protocols TLSv1.2 TLSv1.3; ssl_ciphers HIGH:!aNULL:!MD5;
Add or remove certificates from the following directory:
Run the following commands:
docker compose stop nginx_proxy docker compose up -d
Refer to nginx’s documentation for the standard SSL configuration procedure.
Updating URL/URIs in Keycloak#
Once your SSL cert and key are in place, you will need to update Keycloak to point to your new root URL and any valid URI redirects to your domain.
Navigate to your Keycloak instance at <FQDN>/auth/admin and log in.
Select Clients from the left-hand navigation.
Select repo-service from the list of available clients.
On the Settings tab, update your root URL and any necessary valid redirect URI’s.
Click Save at the bottom of the page.
Select Clients from the left-hand navigation.
Select repo-account-sync from the list of available clients.
On the Settings tab, update your root URL.
Click Save at the bottom of the page.
Rebuilding your channel index#
Migrating from HTTP to HTTPS or updating your FQDN will alter the file path to your channel’s packages. You must rebuild your channel index to correct the file path. If you do not, you will be unable to successfully download packages after migrating.